Explain This: Why Router DNS Hijacks Become Identity Incidents Fast
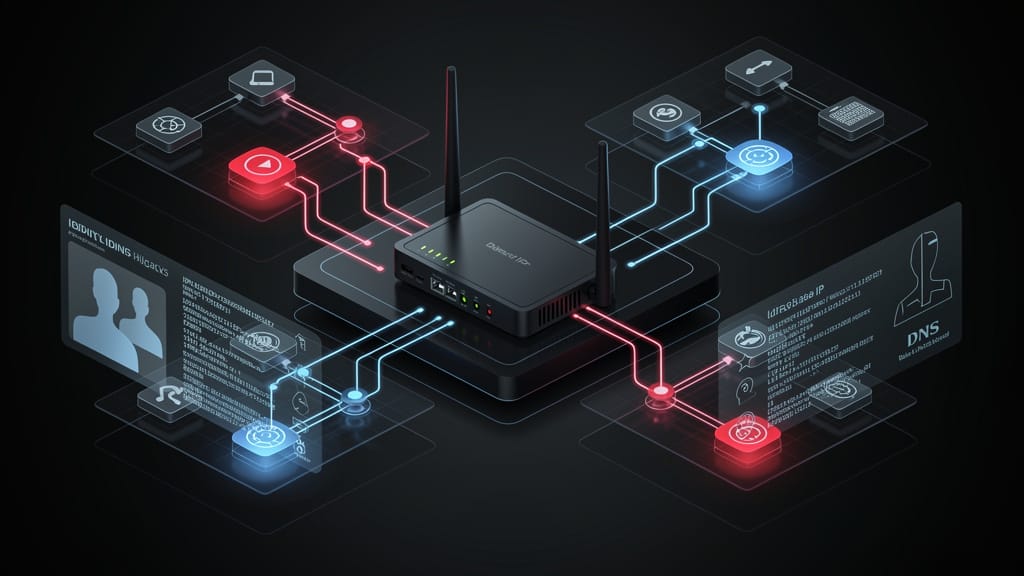
The DOJ router disruption matters because DNS hijacks are not just network events. They are quiet identity incidents with ugly evidence problems.
The Justice Department's court-authorized disruption of a Russian military-run DNS hijacking network landed like another takedown headline. It is more useful than that.
The real lesson is that a compromised router can stop being "just infrastructure" very quickly. Once an attacker controls DNS resolution at the edge, they can steer users into fake login flows, intercept sessions, and make an identity compromise look like a normal authentication problem.
That is the thesis here: DNS hijacking on small office and home office routers is really an identity-control failure in network clothing, and teams that treat it like a niche router issue will underreact.
What It Is
DNS hijacking changes where a user's device goes when it asks for a legitimate service. If an attacker can tamper with a router's DNS settings or route traffic through infrastructure they control, they do not need to break Microsoft 365 directly. They can sit in the middle and manipulate the path to it.
That is why the DOJ action matters. The government said the disrupted network was controlled by a Russian military intelligence unit and used compromised routers to facilitate malicious operations. Microsoft's reporting added the operator detail security teams need: compromised SOHO routers were part of adversary-in-the-middle campaigns that targeted cloud productivity logins.
In plain English, the attacker does not need your password database if they can change the road signs on the way to your login page.
Why It Matters
Security teams often bucket router compromises as commodity noise, especially when the affected hardware sits in branch offices, remote work setups, or unmanaged edge environments. That framing is too small.
A router-level DNS hijack can become four problems at once:
- An account compromise problem, because credentials and tokens are now in play.
- A detection problem, because the activity may look like valid user traffic.
- A scope problem, because multiple users may have trusted the same poisoned path.
- An evidence problem, because the best logs may live on devices nobody was treating as evidentiary systems.
This is where legal and security interests finally line up. If leadership asks whether the incident was contained, you need more than a password reset count. You need to know which routers were exposed, which users authenticated through them, what artifacts exist, and whether your retention model can support a later inquiry.
A policy is not a shield. It is a paper trail.
What to Do This Week
- Inventory internet-facing and branch-office routers that can influence employee DNS resolution.
- Check for unauthorized DNS setting changes, rogue admin accounts, firmware lag, and unexplained management access.
- Treat suspicious router compromise as possible identity exposure, not just a network anomaly.
- Pull sign-in logs for accounts that authenticated through affected locations, then review impossible travel, token anomalies, and MFA fatigue patterns.
- Preserve router configs, management logs, and authentication telemetry before you start cleanup.
- Force credential and session resets where the poisoned-path window cannot be bounded cleanly.
- Decide now who owns edge evidence collection, because this gets messy fast when IT, security, and legal assume someone else has it.
If your remote and branch edges are outside your incident model, this story is your warning. Cheap hardware can still create expensive facts.
Subscribe if you want the legal version of incident response, not the PR version.
Sources
- Office of Public Affairs | Justice Department Conducts Court-Authorized Disruption of DNS Hijacking Network Controlled by a Russian Military Intelligence Unit | United States Department of Justice
- Justice Department Conducts Court-Authorized Disruption of DNS Hijacking Network Controlled by a Russian Military Intelligence Unit | FBI Philadelphia
- SOHO router compromise leads to DNS hijacking and adversary-in-the-middle attacks | Microsoft Security Blog
- US disrupts Russian military-run DNS hijacking network, Justice Department says | Reuters
- r/Ubiquiti discussion: DOJ quietly removed Russian malware from routers in US homes and businesses



